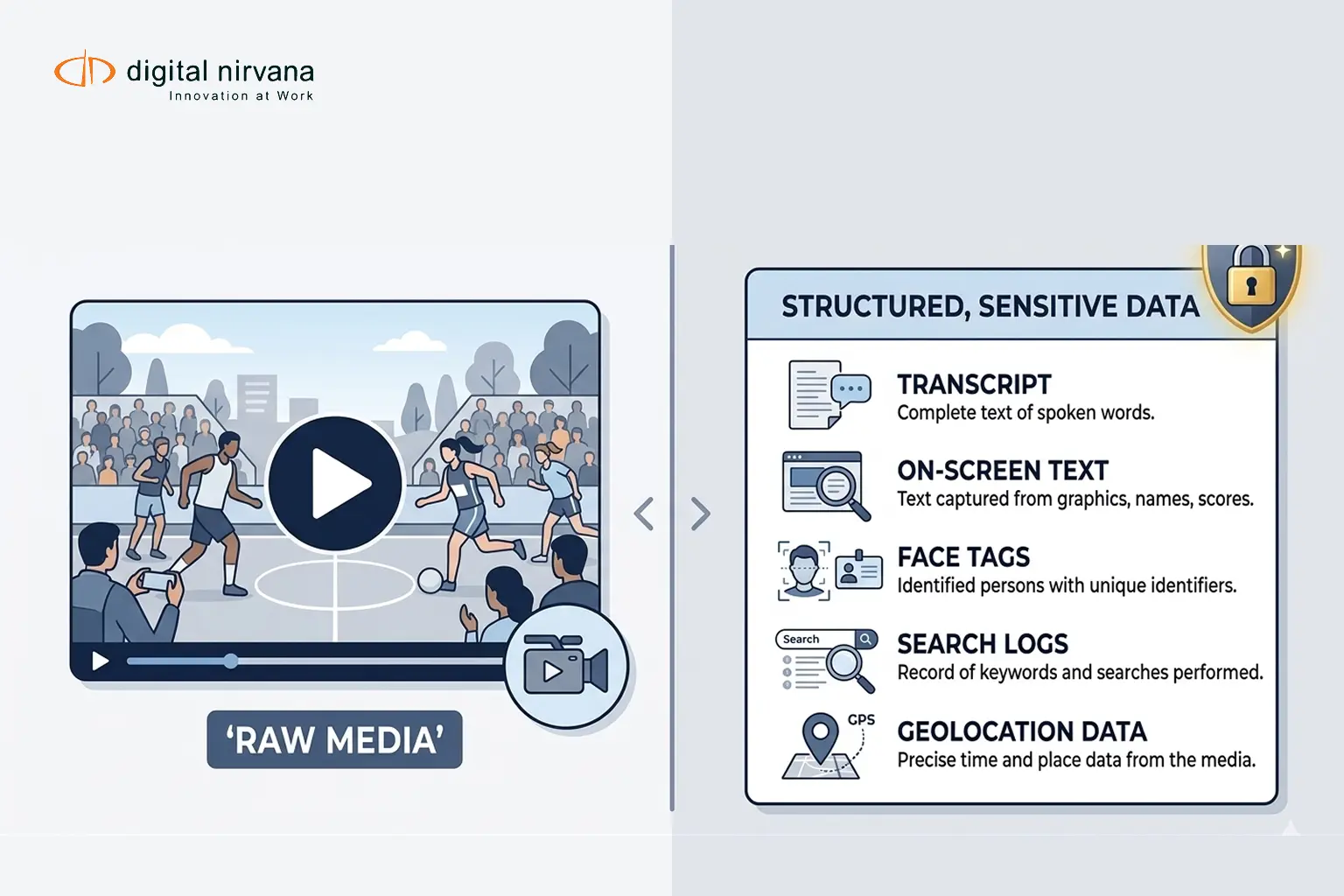
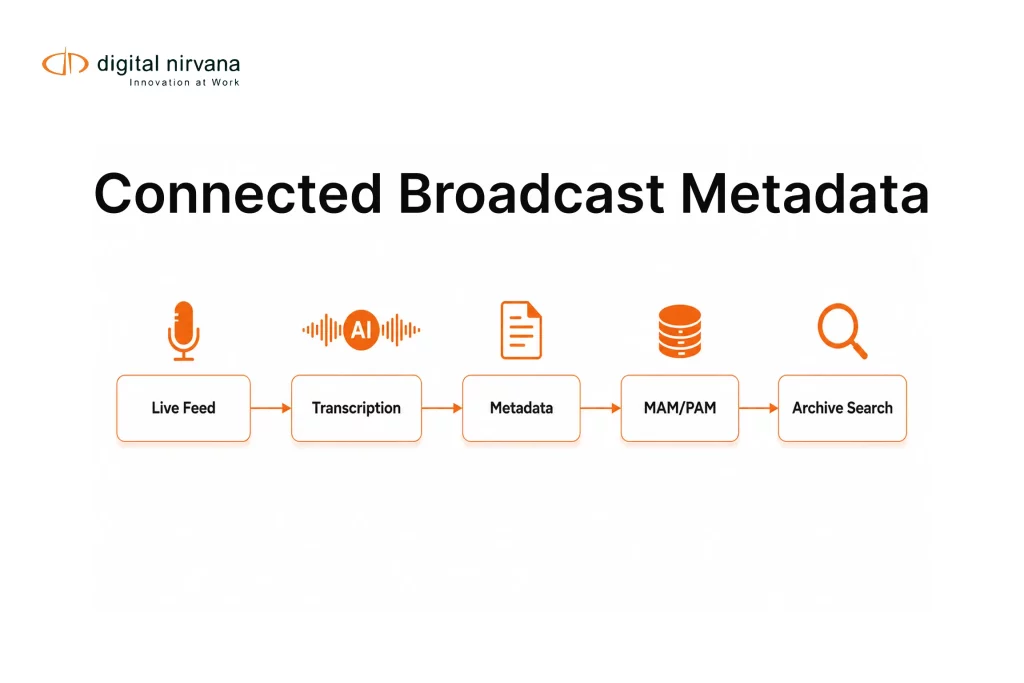
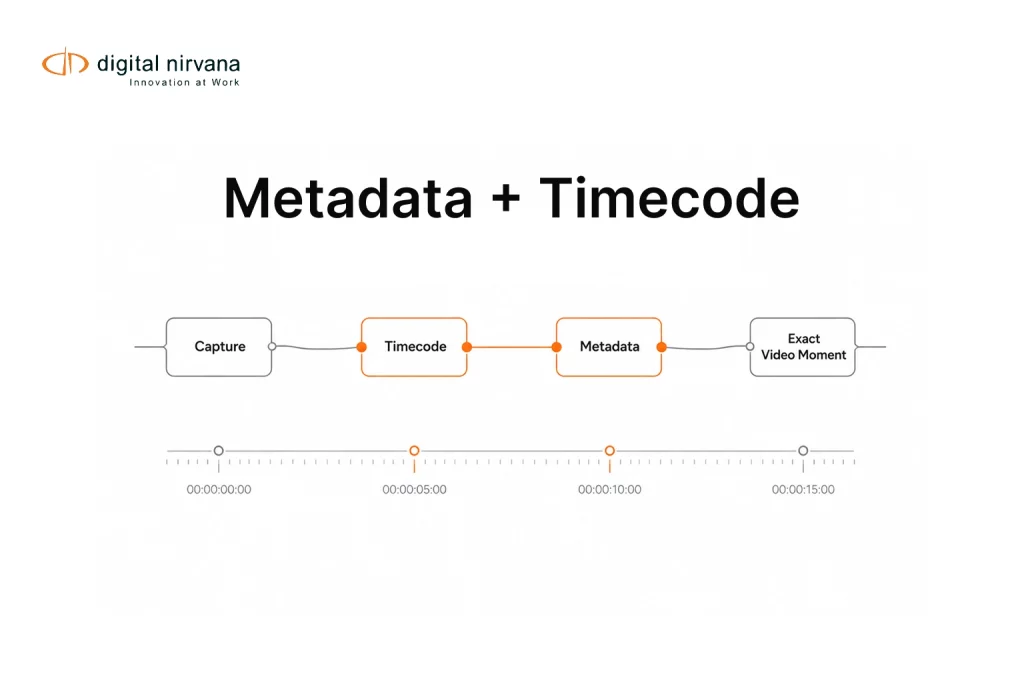
Metadata tagging makes media easier to search, clip, reuse, monetize, and govern. It also creates a new kind of risk: your content is no longer “just video.” It becomes searchable text, named entities, face tags, and timecoded markers that travel across systems.
That is great for speed. It is also why security reviews get intense fast, especially when legal, compliance, and procurement teams start asking about PII, retention, access controls, and SOC 2 readiness.
This checklist is built for buyers evaluating metadata tagging software in real broadcast and media operations, where MAM and PAM integrations, audit trails, and timecoded evidence matter.
Why Metadata Tagging Software Needs A Different Security Lens
Traditional SaaS security reviews focus on customer records, documents, and structured databases. Metadata tagging software adds media-specific surfaces:
- Timecoded transcripts and captions that can include personal data. Under GDPR, personal data is broadly defined as information relating to an identified or identifiable person.
- On-screen text extraction, which can capture names, phone numbers, addresses, ID numbers, and private documents shown on camera.
- Face, speaker, and entity tags that make identity searchable at scale.
- Rule engines that can apply policy decisions across thousands of assets, meaning one misconfiguration can spread quickly.
So the real question is not only “is the platform secure,” but also “can we prove who accessed what, what changed, and why.”
That is where access controls, audit logs, retention policy, and SOC 2 style evidence become central.
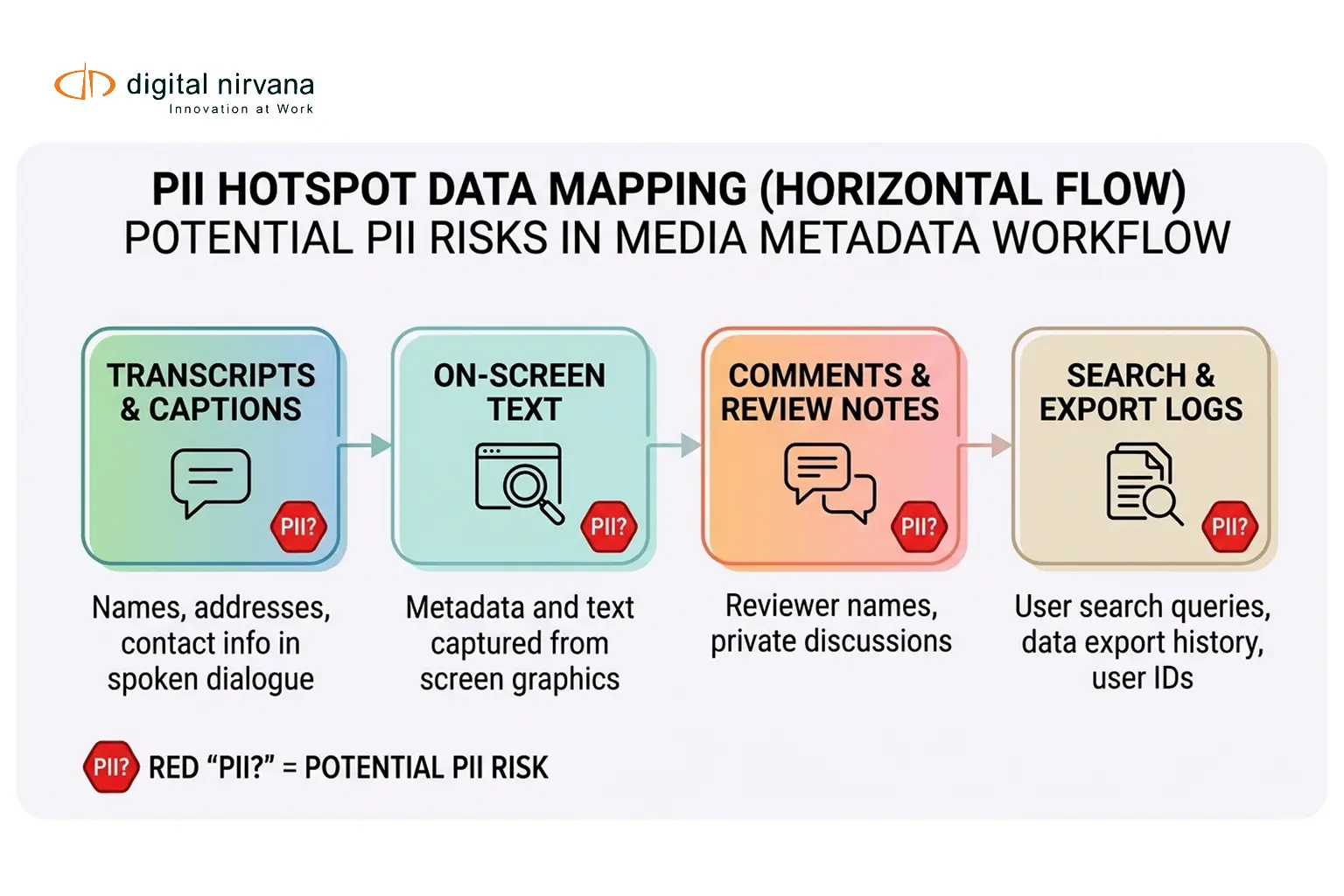
Where PII Hides In Media Metadata
Before you can protect sensitive data, you need to know where it appears.
Common places PII shows up in metadata tagging workflows
- Transcripts and captions
Names, email addresses, phone numbers, addresses, financial references, and other identifiers. Many transcription systems support PII identification and redaction because it is a real risk in transcripts. - On-screen text and graphics
Lower thirds, chyrons, slates, legal disclaimers, medical or legal documents, spreadsheets, device screens, and messages displayed on camera. - Comments, review notes, and annotations
Human notes can include sensitive context, like legal guidance, embargoes, and internal decisions. - Search logs and export logs
Who searched for what, and what was exported, can be sensitive, especially in investigations or rights disputes. Digital Nirvana emphasizes audit-ready logging and governed workflows for defensibility.
If your organization operates under GDPR or similar regimes, retention must be limited to what is necessary, and time limits for erasure or review are expected as a principle.
The Security Checklist
Use this as a practical procurement checklist for metadata tagging software, and as an internal readiness guide for rollout.
Security Checklist Table
| Area | What To Verify | Evidence To Ask For |
| Data Inventory | What data is processed, stored, and generated (transcripts, markers, tags, search logs) | Data flow diagram, data classification list |
| PII Controls | Ability to detect and redact PII from transcripts or derived text | Redaction options, admin controls, test outputs |
| Encryption | Encryption in transit and at rest, plus key management practices | Security architecture overview, key management approach |
| Access Controls | SSO, MFA, RBAC, least privilege, admin separation | RBAC matrix, access review process |
| Audit Logging | Logs for access, exports, tag edits, rule changes, admin actions | Sample audit logs, retention settings |
| Retention And Deletion | Retention policies for media, metadata, logs, backups, legal holds | Retention policy templates, deletion method |
| SOC 2 Readiness | Control coverage across trust criteria and evidence collection | SOC 2 scope guidance, evidence examples |
| Vendor Risk | Subprocessors, DPAs, incident process, breach notification | Subprocessor list, DPA, incident response summary |
Data Minimization And Scope Controls
Security starts with scoping.
- Tag only what you need for your workflow
If legal needs timecoded transcripts but editorial does not need full speaker identity, scope accordingly. - Separate production metadata from sensitive investigative workflows
A different retention and access policy is often needed for high-risk content. - Define your “derived data” policy
Transcripts, markers, embeddings, and search logs are derived data. Treat them as first-class data assets, not exhaust.
GDPR principles reinforce the idea of limiting storage duration and implementing periodic review or erasure timelines.
PII Controls: Detection, Redaction, And Safe Outputs
Minimum PII capabilities to look for
- PII discovery options for transcripts
Some transcription systems support the identification and redaction of PII from transcripts, which can be essential in regulated workflows. - Configurable redaction policy
Your policy should define what is redacted, where redaction applies, and who can override it. - “Export safety” rules
The biggest leaks happen during exports. Ensure exports can be restricted, logged, and watermarked for accountability. A MAM-first security model emphasizes permissions, logging, and enforcement of retention at the asset level.
Practical external reference for teams building transcript PII controls
Amazon Transcribe documents approaches for identifying or redacting PII in transcripts, which is a useful model for how vendors may support transcript safety features.
Encryption And Key Management
Most buyers expect encryption in transit and at rest, plus reasonable key management practices.
Ask for clarity on
- Transport security
TLS for all web, API, and integration paths. - Storage encryption
Encryption for media, derived metadata, and backups. - Key management model
Who controls keys, what rotation exists, and how privileged access is handled.
Access Controls And Identity: RBAC, MFA, Least Privilege
In metadata tagging systems, access is not only about logging in, but it is also about what you can search, preview, export, and edit.
Baseline requirements
- Role-based access control
Roles should map to projects, series, regions, and collections, so teams see only what they should. Digital Nirvana describes role-based access control for editors and producers as part of secure MAM operations. - MFA and strong authentication for high-risk actions
Exporting clips, changing policy rules, and approving compliance tags should require stronger checks. - Least privilege
Least privilege is a widely used security principle for limiting access to what is necessary. NIST’s least-privilege control language is often cited for this practice. - Administrative separation
Separate admin roles for identity, policy, and exports, and ensure admin actions are logged.
For a clean framing reference, CIS highlights access control management and account management as core security controls.
Audit Logs, Governance, And Evidence Quality
If you want SOC 2 readiness, you need verifiable evidence. SOC 2 is explicitly about controls relevant to security and related criteria.
In metadata operations, that means logging more than logins.
You want logs for
- Content access and preview
- Search activity for sensitive cases
- Exports and downloads
- Tag edits, including before and after values
- Rule changes, confidence threshold changes, and model version changes
Digital Nirvana’s governance guidance for metadata automation is a strong model here, especially the focus on audit trails that record who changed what, when, and why.
For retention of audit records, many programs align with the idea that audit records must be retained until no longer needed for legal, audit, or operational purposes.
Retention, Legal Holds, And Secure Deletion
Retention policy is where security, compliance, and operations collide.
Build a retention plan across four layers
- Primary media
- Derived metadata (transcripts, tags, markers, embeddings)
- Operational logs (access logs, export logs, system logs)
- Backups and archives
GDPR storage limitation guidance requires data to be kept only as long as necessary, with time limits for erasure or review.
Media teams also need legal holds
If a dispute or investigation exists, deletion may be paused. Your system should support this cleanly, without ad hoc workarounds.
Vendor Risk, Subprocessors, And Contracts
Even if your metadata tagging vendor is strong, their subprocessors matter.
Ask for
- Subprocessor list and change notification
- Data processing agreement terms
- Incident response and notification timelines
- Support model for security events
SOC 2 vendor management discussions often emphasize keeping evidence of vendor monitoring and contract terms, because auditors want proof that the process exists and is used.

SOC 2 Readiness: How To Align Controls With Evidence
SOC 2 is an examination report on controls relevant to security and other trust services criteria, designed for service organizations handling customer data.
The most common readiness failure is not a missing tool; it is missing evidence.
What Evidence Looks Like In Practice
Auditors commonly look for documentation, logs, policies, and system outputs that demonstrate the controls are operating.
For metadata tagging software rollouts, that translates into evidence such as
- Access review records
Who reviewed access, how often, and what was changed. - Audit log samples
Export logs, admin action logs, and tag edit logs. - Change management evidence
Rule changes, threshold adjustments, model updates, and approvals. - Retention policy and enforcement proof
Screenshots or exports showing retention settings, plus sample deletion events.
If you need the formal framing, the AICPA publishes Trust Services Criteria resources that define the criteria used in these examinations.
Vendor Questions To Ask Before You Buy
Use these questions to compare metadata tagging software vendors and to speed up procurement reviews.
PII And Derived Data
- What PII controls exist for transcripts and extracted text, including redaction and overrides?
- What derived data is stored, where, and for how long.
- Can we disable certain outputs, like face identity tags, while keeping others?
Retention And Deletion
- Can retention be configured separately for media, derived metadata, and logs?
- How do legal holds work?
- How is deletion performed, and does it include backups?
Access Controls
- Do you support SSO and MFA?
- Can permissions be applied at the asset and collection level, aligned with MAM practices?
- Do admin roles support the separation of duties?
Audit Logs And Governance
- Are all metadata edits and rule changes audited, including before-and-after values?
- Can we export logs for SIEM or compliance tools?
- Do you provide governance dashboards that flag missing tags, inconsistencies, and failed checks?
SOC 2 And Audit Readiness
- Do you have a current SOC 2 report, and what is the scope?
- How do you support evidence collection, like access reviews and log retention?
Where MetadataIQ Fits In A Secure Media Stack
MetadataIQ is positioned as a media indexing and integration layer that generates time-coded metadata across video and audio and writes governed outputs back into production environments.
Capabilities that matter for security and governance reviews
- Governance dashboard and quality scoring
MetadataIQ describes tracking, scoring, and auditing metadata health, including flagging failed rule checks before they become compliance issues. - Compliance tagging and rules engine
Useful when policy-sensitive tags and disclaimers need consistent handling. - Audit-ready workflows
Digital Nirvana’s governance approach emphasizes audit trails for metadata changes, including who changed what and when, plus model and ruleset versions. - MAM-first operational alignment
Digital Nirvana’s secure MAM integration guidance emphasizes asset-level permissions, logging every access, and automatically enforcing retention rules, which is the right direction for media teams.
Meet Digital Nirvana At NAB Show 2026
If you’re heading to NAB Show 2026, stop by to see how Digital Nirvana helps teams automatically turn live and recorded video into structured, searchable intelligence. You’ll get a workflow-focused look at how MetadataIQ supports faster review, better discovery, and smoother handoffs across production, compliance, and distribution.
You can meet the team at Booth N1555 in Las Vegas, April 19–22, 2026. If you want dedicated time, book a demo slot ahead of the show.
FAQs
Focus on PII controls for transcripts and extracted text, strong RBAC with least privilege, export restrictions, audit logs for tag edits and rule changes, and retention controls that match compliance needs.
Yes. Transcripts and on-screen text extracts can contain personal data, which is broadly defined under the GDPR as data relating to an identified or identifiable person.
Separate retention by data type, define review and deletion timelines, and support legal holds where needed. Regulators commonly expect time limits for erasure or periodic review under storage limitation principles.
SOC 2 is about controls relevant to security and other trust services criteria, and being able to show evidence that those controls are designed and operating. Auditors look for documentation, logs, and system outputs.
Because metadata changes affect compliance, rights decisions, and search trust. Audit trails make edits and approvals explainable, including who changed what and when.
Conclusion
Metadata tagging software can be a major accelerator for production and compliance, but only if security and governance are built into the rollout. The right approach treats transcripts, tags, and timecoded markers as sensitive data, enforces asset-level access controls, and keeps audit-ready logs that stand up in reviews.
Key Takeaways
- Identify where PII appears in derived metadata, especially transcripts and extracted on-screen text.
- Enforce least privilege with role-based permissions, and require stronger authentication for exports and admin changes.
- Treat audit logs as core evidence, including tag edits, rule changes, and export activity.
- Build retention by layer, and align it with storage-limited expectations and the realities of legal hold.
- If SOC 2 readiness matters, prioritize evidence collection workflows, not just tools.